Why hackers can steal from DeFi?

DeFi, at the time of writing of this article, has over $65 billion dollars in Total Locker Value (TLV) according to DeFi Pulse. More than $230M were lost to hackers and scams in 2020 alone. This year's number is only increasing, and we already saw multi-million hacks and rug pulls happened.
Why is it so enticing for black hats to exploit Blockchain applications? Didn't blockchain supposed to be secure, and we shouldn't be worried about anything? The answer to that is a bit more complicated than we think.
Why hack DeFi applications in the first place?
Decentralized finance (DeFi) has been an exploding trend in the crypto industry for a while now. DeFi apart from being decentralized wants to be also open, so they share their codebase on GitHub for free and for everybody to see. Even if projects weren't doing that, anybody could see smart contracts on-chain on etherscan. If contracts are verified(to improve confidentiality), which is often a case, a smart contract code is available. For a hacker, that's like receiving keys to a bank vault. He can poke around and see what breaks, what doesn't and deduct if he can benefit from things he can break.
Let's not forget the incentives to steal crypto assets are massive due to the nature of cryptocurrencies. They are decentralized, and anonymity is an option that many desire. Mixers are becoming more usable and common. Crypto value is booming, and DeFi daily trading volume is counted in billions.
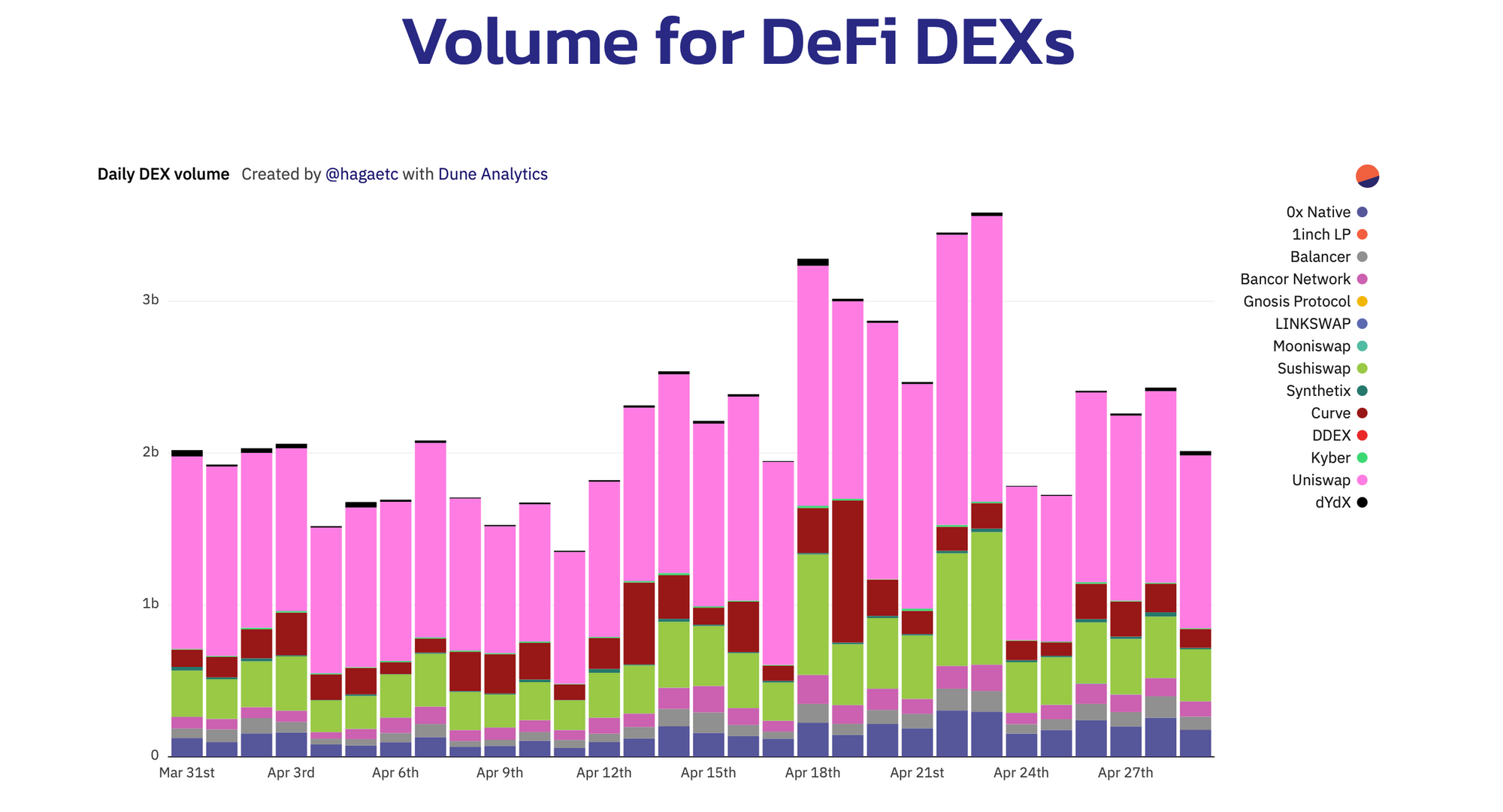
With high trading volume and TLV, protocols working autonomously for the most part, and all is happening publicly with code being available to everybody, DeFi has made itself a vulnerable, lucrative target for malicious hackers.
Why is it possible to hack smart contracts?
Smart contracts are nothing more than scripts that live on-chain, and anybody can interact with them, read them, and use them. This alone makes it hard to protect.
People are responsible for creating software, and software runs on a machine told what to do. It's not a software fault the logic had a loophole, and it's a software engineer's fault. With a public blockchain, it's an even harder job to mitigate programmer errors as code is open by default and everyone sees vulnerabilities. What lives on a blockchain stays on a blockchain. Nothing can be taken down, and updating smart contracts on-chain is not a trivial task. There are frameworks and tools for that, but upgradability (patching smart contracts) comes with its own set of challenges and pitfalls.
Public blockchain (Ethereum) is also a very hostile environment, as Dan Robinson has experienced. Ethereum is a dark forest is a great read and introduction into the MEV concept but to summarize in few words. As soon as a vulnerability is exploited, it becomes visible to many parties simultaneously. They will act on that knowledge and try to beat you to the finish line in executing the transaction.
There are few reasons why smart contracts are hard to protect. The above is just a tip of an iceberg.
- Blockchain as a whole is still young as technology and smart contracts are even more youthful. There aren't many developers with years of experience to guide junior devs. Tooling is still developing and what we have now is nowhere near the tools of other programming languages.
- This one is similar to the previous one, but the smart contract developers are scarce, and it's hard to hire a good one. Most of them are self-taught. Projects are wanting to hire good developers are fighting to get one. Software developers coming from traditional backgrounds into this space often lack a broader perspective on the matter and are simply not aware of many attack vectors.
- Copying code, aka forking, is standard practice in DeFi space. Everybody wants to get a piece of DeFi cake, and new projects copy code they don't truly understand, whereas original developers spend months/years creating the original codebase. The issue is two-fold here. If an initial code that is being forked has a vulnerability, all the forked code will also have the same vulnerability. Another problem is altering the code and introducing vulnerability by mistake or on purpose, creating a back door to steal user funds.
- Smart contracts are compostable, which means they can interact with each other. This composability is the feature driving DeFi innovation. That's why we call it also a "money lego" as everything can be built upon previous projects. This, unfortunately, introduces more complexity and more attack surface, guaranteeing new, unforeseeable attack vectors and risks we wouldn't have thought about in the scope of only one project.
- DeFi smart contracts, as the name suggest, deal almost entirely with money, so any vulnerability makes all of that money at risk.
Running a DeFi project is like climbing without any equipment. One small mistake, and the results are catastrophic.
The future of DeFi hacks.
All of the above sound scary, but that's just the reality of this space. We will see many more hacks surface, mainly from the new projects coming to play and not knowing how to secure their contracts or scam projects to steal your funds. We're in a significant FOMO phase in crypto and DeFi. Everybody wants in as they fear they will miss out. Rash decisions are never good.
More people are aware, especially developers, about issues and challenges with smart contracts. More people are being educated about challenges, and Blockchain space is growing and getting more traction every day. In few years, hacks like this will be only a memory as we will see stable and secure DeFi protocols.
