What happens when you don’t test enough?

Looking at the number of exploits I already covered, you can guess what I’m alluding too. You’re right. You get REKT! But sometimes you also get lucky…somewhat.
Credit goes to @Mudit__Gupta for reporting this on Twitter.
Wild Credit was exploited for ~$650k, but all of this would not have happened if some basic precessions were taken on access restriction for initialize() function.
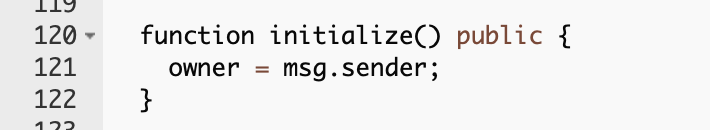
That means everyone can call this function and become an owner of the LP Token Contract. The owner can freely mint and burn LP tokens, and that what has happened.
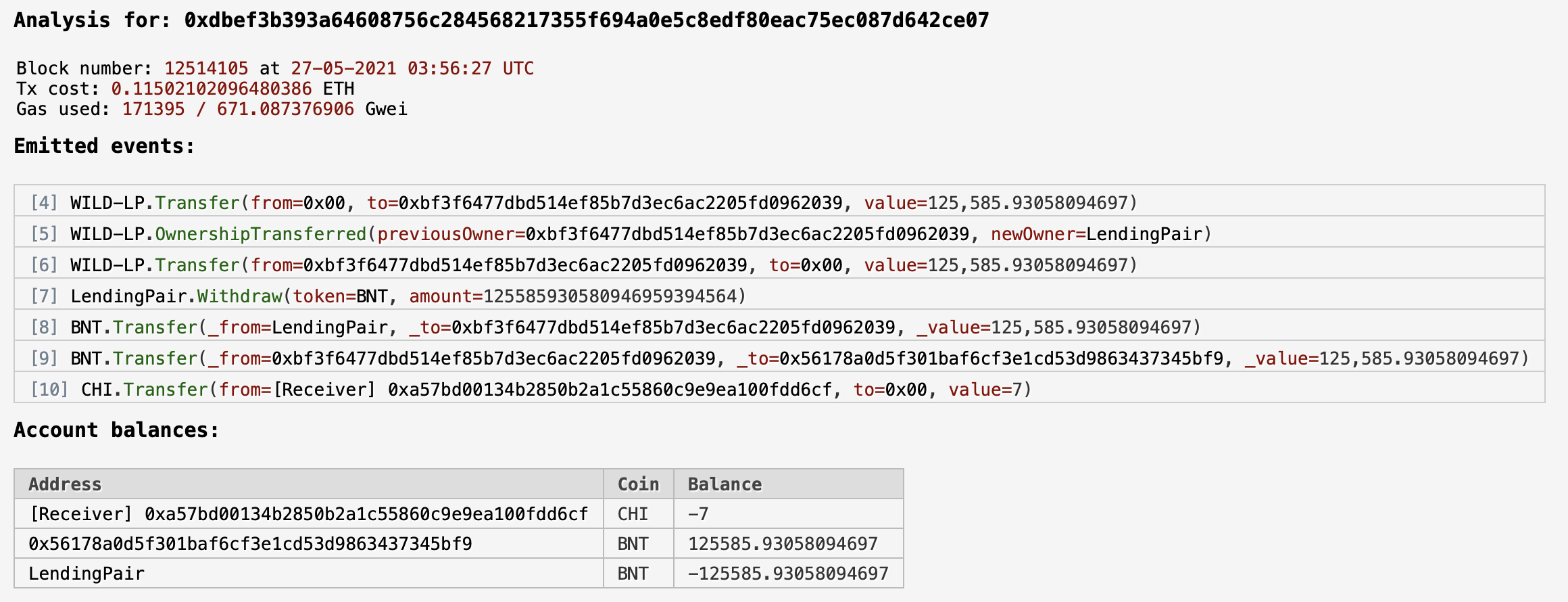
- Attacker called
initialize()becoming an owner - Minted ~125k of BNT tokens to himself
- Withdrawn minted tokens
Details about the exploit transaction can be found below
What is interesting, the funds were returned. But not by an actual attacker, only by an operator of a generalized front-running bot that front-run an actual attacker.
The "attacker" who returned the funds was actually an operator of a generalized front-running bot.
— WildCredit (@WildCredit) May 27, 2021
The real attacker attempted to execute their exploit here and was front-run:https://t.co/NjYpoiciKr
Test, test, test, audit and test, test, test
It’s easy to get lost in the details of checking the edge cases, but we lose sight of the real point of testing. To test if everything, even basic things, is also covered and working as intended. We write unit tests for ourselves to feel sane. Always aim for 95%-100% of code coverage with tests so things like that will never happen.
Not always you can get this lucky, but as Mudit Gupta has said
“An audit or even a peer review from a decent dev would have prevented this issue.”
Stay safe out there and write tests.
Thanks for reading, and if you like my writing, you can subscribe to my blog to receive the daily newsletter as I’m currently in the middle of 100 days of blogging challenge. Subscription box below 👇
If the newsletter is not your thing, check out my Twitter @adrianhetman, where I post and share exciting news from the Blockchain world and security.
See you tomorrow!
